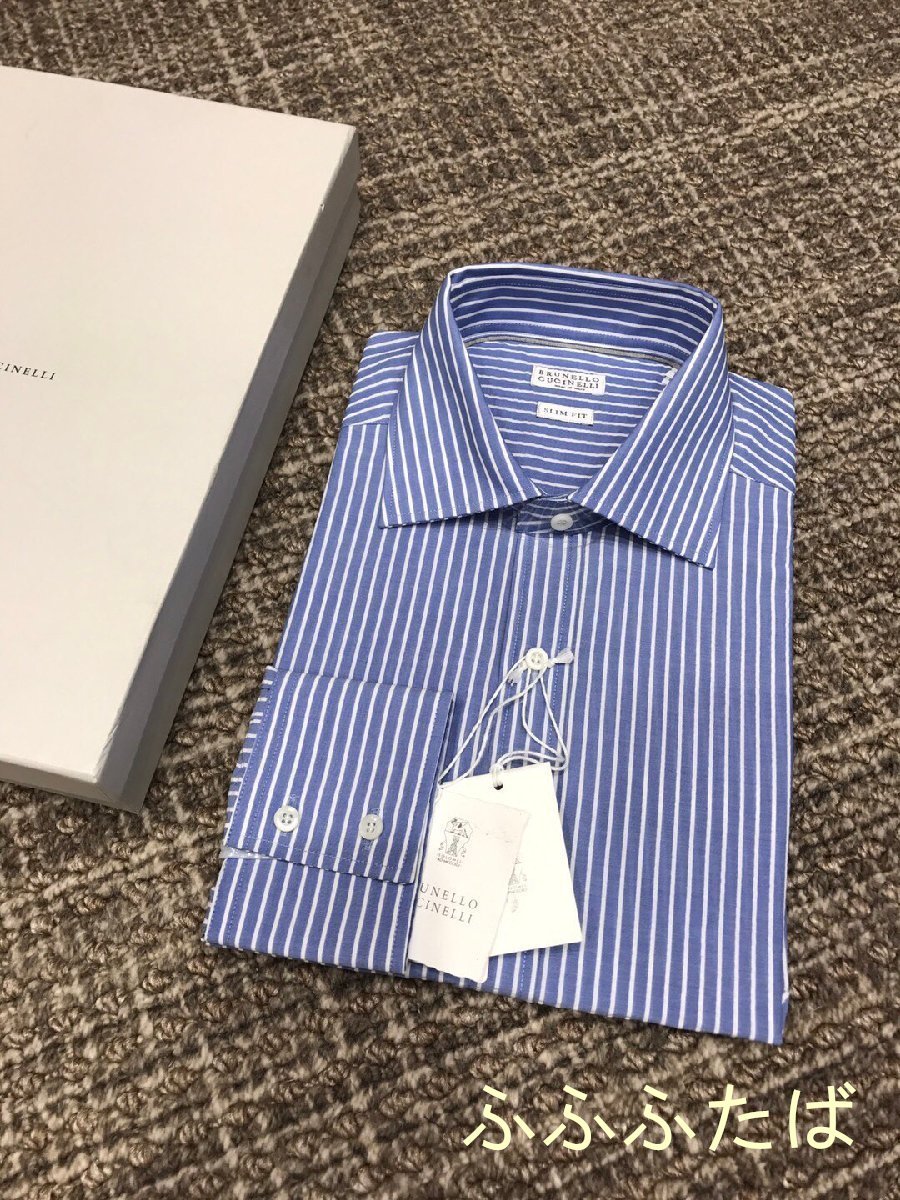
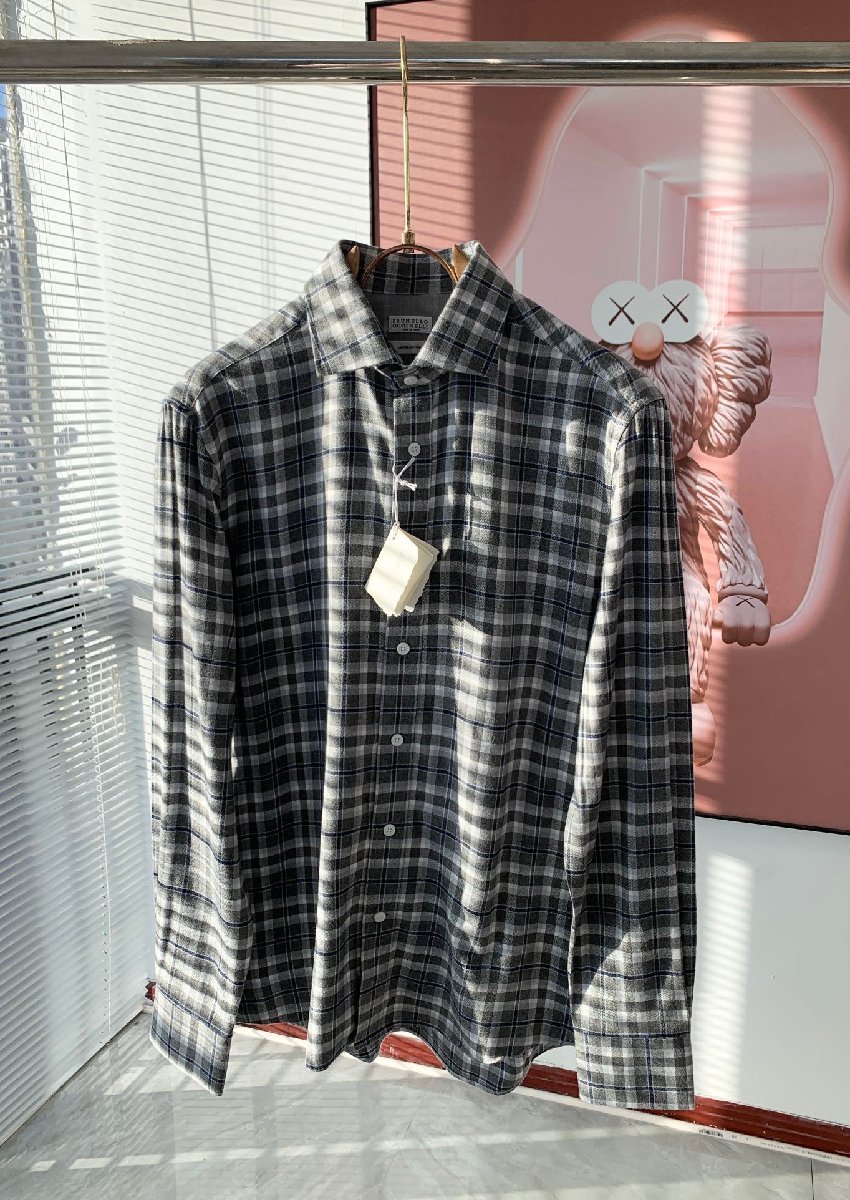
ブルネロクチネリ 長袖シャツ サイズXL -
(税込) 送料込み
商品の説明
商品説明
[カテゴリ]シャツ
[ブランド]
BRUNELLOCUCINELLI(ブルネロクチネリ)
[商品名]
-
[型番]
-
[男女別]
メンズ
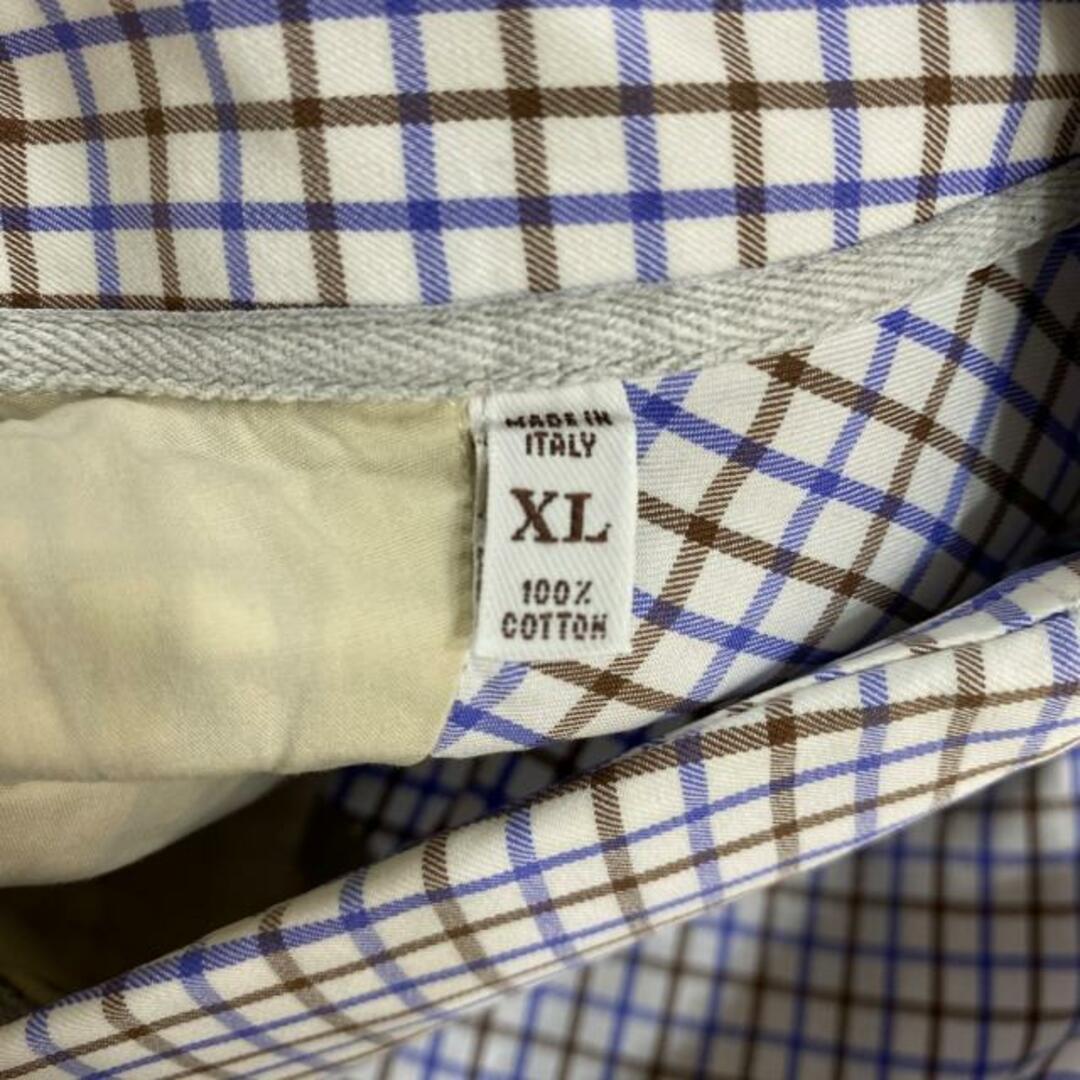
[表記サイズ]
XL
[実寸サイズ]
肩幅:約50cm
袖丈(ゆき丈):約67cm
身幅:約58cm
着丈:約80cm
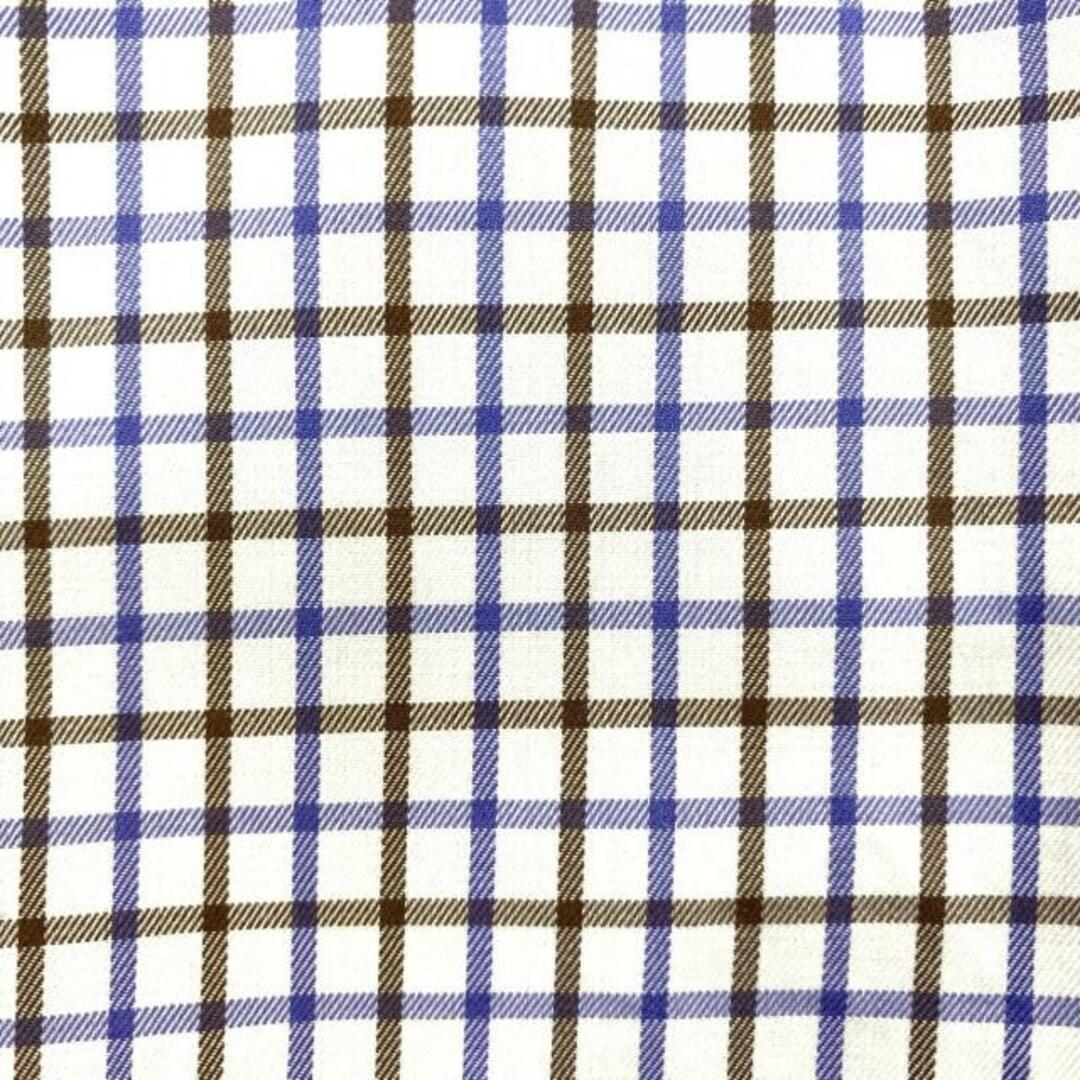
[カラー]
白×パープル×ダークブラウン
[デザイン]
チェック柄
[コンディションの備考]
【本体】
・全体的⇒薄っすらと汚れている
【特記事項】
・保存時のニオイあり
[製造番号・刻印]
-
[シリアル]
***
[付属品]
なし
こちらの商品はラクマ公式パートナーのBrandear(ブランディア)によって出品されています。
以下の内容のお問い合わせについてはお返事ができませんのであらかじめご了承ください。
・商品状態の確認(汚れ具合、形状の確認等々)
・お値下げの交渉
8580円ブルネロクチネリ 長袖シャツ サイズXL -メンズトップスメンズ カジュアルTシャツ&ポロシャツ | Brunello CucinelliBRUNELLO CUCINELLI - ブルネロクチネリ 長袖シャツ サイズXL -の通販
着丈66ブルネロクチネリ コットンジャージーシャツ - シャツ
贅沢屋の Brunello Cucinelli ブルネロクチネリ シャツ 夏新品
メンズ カジュアルTシャツ&ポロシャツ | Brunello Cucinelli
最初の BRUNELLO 秋冬着 コットン 2XLサイズ チェック柄 綿 カジュアル
レディーストップ、Tシャツ、ポロシャツ | Brunello Cucinelli
レディーストップ、Tシャツ、ポロシャツ | Brunello Cucinelli
ブルネロクチネリ チノパン46サイズ
メンズ カジュアルTシャツ&ポロシャツ | Brunello Cucinelli
BRUNELLO CUCINELLI - ブルネロクチネリ 長袖シャツ サイズXL -の通販
トップスブルネロクチネリ 長袖シャツブラウス XS - - シャツ/ブラウス
ブルネロクチネリ公式ブティック
新品の ブルネロクチネリ 長袖カットソー サイズXL Tシャツ/カットソー
ブルネロクチネリ 長袖シャツ LEISURE FIT メンズ SIZE XS (XS以下
BRUNELLO CUCINELLI ブルネロクチネリ BDシャツ | localcontent.gov.sl
BRUNELLO CUCINELLI - ブルネロクチネリ 長袖シャツ サイズXL -の通販
雑誌掲載 BRUNELLO CUCINELLI スナップボタン ヨーク 長袖シャツ
brunello cucinelli ジャケット グレージャケット/アウター
ブルネロクチネリ 長袖シャツ LEISURE FIT メンズ SIZE XS (XS以下
ブルネロクチネリ公式ブティック
BRUNELLO CUCINELLI - ブルネロクチネリ 長袖シャツ サイズXL -の通販
お手頃 ブルネロクチネリ 長袖シャツ サイズXL - | skien-bilskade.no
ブルネロクチネリ グレージュとシャンパンシルバーTシャツXS-
表記サイズXS美品 ブルネロクチネリ BRUNELLO CUCINELLI シャツ ボタン
ブルネロクチネリ 長袖シャツ LEISURE FIT メンズ SIZE XS (XS以下
楽天市場】【訳あり】【XL】 BRUNELLO CUCINELLI ブルネロクチネリ
楽天ランキング1位】 BRUNELLO CUCINELLI(ブルネロ T-シャツ 長袖 丸首
トップスブルネロクチネリ 長袖シャツブラウス XS - - シャツ/ブラウス
2022激安通販 麻 カジュアルシャツ トップス メンズ 長袖 リネンシャツ
ブルネロクチネリ白シャツレディース - zincattotelhas.com.br
ブルネロクチネリ 長袖シャツ LEISURE FIT メンズ SIZE XS (XS以下
ブルネロクチネリ グレージュとシャンパンシルバーTシャツXS-
BRUNELLO CUCINELLI - ブルネロクチネリ 長袖シャツ サイズXL -の通販
お手頃 ブルネロクチネリ 長袖シャツ サイズXL - | skien-bilskade.no
表記サイズXS美品 ブルネロクチネリ BRUNELLO CUCINELLI シャツ ボタン
メンズ カジュアルTシャツ&ポロシャツ | Brunello Cucinelli
美品【ブルネロ クチネリ】高級コットンカットソー立ち襟デザイン
楽天市場】BRUNELLO CUCINELLI(ブルネロクチネリ) サイズ:S LEISURE
着丈66ブルネロクチネリ コットンジャージーシャツ - シャツ
レディーストップ、Tシャツ、ポロシャツ | Brunello Cucinelli
商品の情報
メルカリ安心への取り組み
お金は事務局に支払われ、評価後に振り込まれます
出品者
スピード発送
この出品者は平均24時間以内に発送しています